
What is Spear Phishing?
Amid the ever-mutating realm of digital hazards, spear phishing emerges as an especially sly form of cyber-attack, meticulously designed to mimic reliable entities with the
These articles and videos have been published by eSudo, a local IT support and Consulting company (MSP) in Silicon Valley, San Jose, CA, and the San Francisco Bay Area over 22+ years to educate our community about common questions on today’s technology and cybersecurity trends.
Contact us today for a complimentary consultation if you have a question about your business challenges!
Contact Us for a free technology assessment, or to discuss how we can make technology work for your San Jose business or call us at 408-216-5800 for immediate computer repair

Amid the ever-mutating realm of digital hazards, spear phishing emerges as an especially sly form of cyber-attack, meticulously designed to mimic reliable entities with the

Do you know the biggest cybersecurity risk affecting your law firm? Are you confident that your technology is providing end-to-end security and meeting compliance? If
Understanding HIPAA Incidental Disclosures: Examples and Best Practices HIPAA (Health Insurance Portability and Accountability Act) regulations are crucial for safeguarding sensitive patient information. However, despite

Businesses running Windows Server 2008 or 2012R2 needs to upgrade to Windows Server 2016 or Windows Server 2019 because it is no longer supported by
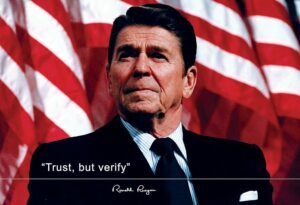
Ronald Reagan made the phrase “Trust but verify” famous during his discussion with the Soviet Union on nuclear disarmament in 1987. This concept still holds

Have you spent years building your LinkedIn profile? It’s a valuable asset for you and your company. But have you taken steps to protect it

Is your business still using software from the Stone Age? Your cyber insurance provider might be seeing red flags. Dive into our visual guide to

The Imperative of a Robust Offboarding Process: Safeguarding Your Business in a Dynamic Landscape As we kick off the new year, businesses are unfortunately having

Starting February 1st, 2024, major changes to email authentication by Google and Yahoo could affect your clients’ emails. The purpose of the change to prevent