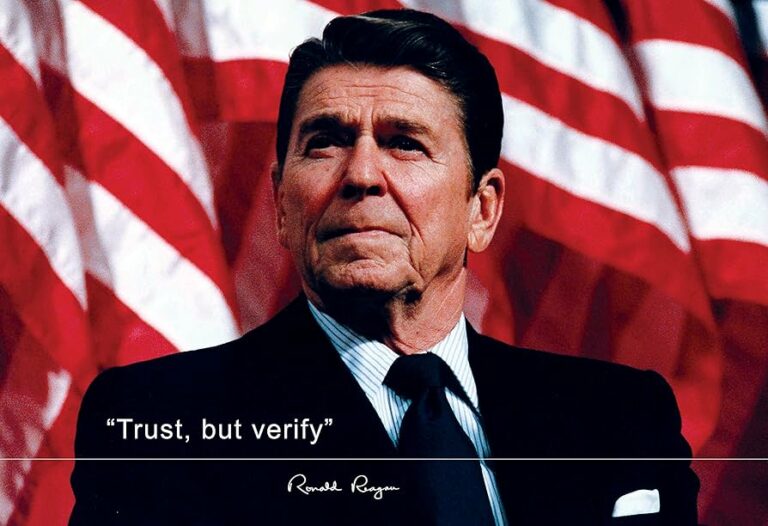
Ronald Reagan made the phrase “Trust but verify” famous during his discussion with the Soviet Union on nuclear disarmament in 1987. This concept still holds true today regarding cybersecurity and how you can use it to protect yourself from cybercriminals.
What is social engineering?
Social engineering refers to the manipulation tactics cybercriminals use to deceive people into giving out confidential information. The core strategy relies on exploiting human tendencies to trust and help others. However, you can shield yourself from exploitation by understanding common social engineering schemes, verifying requests, and practicing cyber vigilance.
Let’s delve into a real-world example to illustrate this concept:
Imagine receiving a phone call from your internet service provider from someone claiming to be a technician. They inform you that your router has been compromised and urgently request remote access to fix the issue. Despite feeling hesitant, you comply, believing the caller’s authoritative demeanor and concern for your security.
Little do you know, you’ve just fallen victim to a social engineering ploy that grants the attacker unrestricted access to your network.

Now that we understand the threat, let’s explore how we can defend ourselves against it.
The Concept of “Trust but Verify”: A Shield Against Deception
In the realm of cybersecurity, the mantra “trust but verify” serves as a powerful defense mechanism against social engineering attacks. It encourages us to maintain a healthy level of skepticism, validating the authenticity of requests or communications before taking any action.
Here’s how you can apply this principle to safeguard yourself from social engineering:
- Question the Unexpected: If you receive an unsolicited email, message, or phone call requesting sensitive information or urgent action, pause and question its legitimacy. Verify the identity of the sender or caller through independent means, such as contacting them directly through a trusted channel or consulting with a colleague.
- Scrutinize Communication: Pay close attention to the language, tone, and context of communications. Be wary of messages that evoke urgency, fear, or curiosity, as these are common tactics used by social engineers to prompt impulsive actions. Look for inconsistencies or red flags that may indicate a fraudulent attempt to deceive you.
- Verify Identities: When interacting with unfamiliar individuals or entities, verify their identities before disclosing sensitive information or granting access to systems or resources. Request official credentials or contact information and independently verify them through reputable sources or official channels.
- Practice Vigilance: Cultivate a culture of cybersecurity awareness within your organization or community. Educate yourself and others about the tactics and techniques used by social engineers, empowering everyone to recognize and report suspicious behavior. Remain vigilant and report any potential threats or incidents to your organization’s cybersecurity team or authorities.
Conclusion: Fortifying Your Digital Fortress
In the dynamic landscape of cybersecurity, vigilance and preparedness are our strongest allies. By embracing the principle of “trust but verify” and instilling a culture of cybersecurity awareness within your organization, you can fortify your defenses against social engineering attacks and safeguard your company’s valuable assets.
Remember, as business leaders, the security of our organizations rests in our hands. Let us unite in our commitment to protecting our businesses from the perils of digital deception, standing firm against the forces of cybercrime and ensuring a safer and more secure future for all.
Together, we can confidently navigate the complexities of the digital world, knowing that we have taken proactive steps to defend our businesses against the ever-present threat of social engineering.
Related Articles:
Frequently Asked Questions
At eSudo, we help your law firm, accounting practices and small business feel like a big business when it comes to technology. For over 23+ years, we give you all the tools and support you need without the cost of hiring extra staff. That means if things go wrong, you don’t have to worry about layoffs or added expenses.
Our IT services give you the power of a large business at a fraction of the cost, helping you stay competitive in today’s digital world. With us, your business can compete with the big players and make more money while staying secure and efficient.
We specialize in working with professional service organizations like law firms, accounting firms (CPAs), and wealth management. However, eSudo have helped other business such as non-profit organizations, manufacturing and other small businesses after we have reviewed their needs and determined if they are good fit for our services.
eSudo is not a traditional computer support company; we focus on security first, and computer support happens to be part of the security services. In the dynamic landscape of network security, a proactive approach is key to safeguarding your business. It’s not a one-time event but an ongoing commitment to keep your systems resilient against evolving threats. With the rise of a mobile workforce and the omnipresence of phishing attempts or social engineering or AI, educating your employees, continuous monitoring and proactive support are vital to prevent data breaches.
If your business is looking for break-fix support or hourly IT services, we may not be for you because we cannot fully manage your risks and more importantly, it creates a trust issue in our relationship. Under a “break-fix” model, there is a fundamental conflict of interest between your business and eSudo.
“Over 97% of American businesses in 2023, operating in a digitally-driven landscape, heavily rely on the Internet for essential functions such as productivity, performance optimization, streamlined communication, bolstered sales, and various other facets of their daily operations. This heightened dependence on digital infrastructure, however, comes with a notable caveat: more than 87% of small businesses are entrusted with customer data that could be potentially compromised in the event of a cyberattack.”
We keep your IT Systems running and data secure with our proven IT Strategy, Managed Security, and Proactive Support & End User Management. Our Strategy focuses on identifying, prioritizing, and recommending the right technology for your organization. Our Managed Security includes data backup, device encryption, zero-trust access management, and policies & procedures. Our Support includes a live phone help desk, 24/7 monitoring, on-site support as needed, employee onboarding, and asset procurement.
Proven track record: We have been building our loyal customer base since 2001 in an industry where IT consulting firms come and go. Our customers, vendors, and employees stay with us because we build and value long term relationships with them. With operations all over the San Francisco Bay Area, eSudo provides reliable IT support to Northern CA-based businesses and beyond. We’re big enough to offer the facilities, services, and expertise you expect and small enough to provide the support and attention you deserve.
People & Process: Over the last 22+ years, we have created and adopted a proven process to ensure success in our operations and have trained our people to follow our proven process to provide consistent results for our customers.
Quality: We do not sell what we have not used or have tested. We recommend industrial and commercial-grade products for small businesses to provide uptime and reliability for our customers.
Responsiveness: A live person will answer your call, and emergency response time is one hour or less guaranteed. We use the most current remote support technology which lets us log in to your computers remotely to address many issues without the need to wait for a technician to come on-site.
This is a very difficult question to answer because not all environments are the same, we will do our best to explain some general pricing guidelines.
For a business with 10 to 50 employees, IT support is a crucial investment to ensure smooth operations and data security. This support includes system maintenance, cybersecurity measures, help desk services, data backup, and software updates. As an IT manager and business owner, allocating a reasonable budget for IT support is essential to prevent downtime, protect against cyber threats, and ensure the firm’s efficiency and success in the digital era. Neglecting IT support can lead to potential vulnerabilities and higher costs in the long run. Thus, viewing IT support as a necessary investment is vital for sustaining your firm’s operations effectively and securely.
A typical price for IT Support and Cybersecurity ranges from $185 to $300 per user per month. Actual cost will be determined after we meet and perform an assessment of your environment.

