
What Should I Consider Before Switching to A New IT Provider or MSP?
Ever wondered if your IT provider is holding back your business growth? Recent studies show that a seamless transition to a new IT provider can
These articles and videos have been published by eSudo, a local IT support and Consulting company (MSP) in Silicon Valley, San Jose, CA, and the San Francisco Bay Area over 22+ years to educate our community about common questions on today’s technology and cybersecurity trends.
Contact us today for a complimentary consultation if you have a question about your business challenges!
Contact Us for a free technology assessment, or to discuss how we can make technology work for your San Jose business or call us at 408-216-5800 for immediate computer repair

Ever wondered if your IT provider is holding back your business growth? Recent studies show that a seamless transition to a new IT provider can
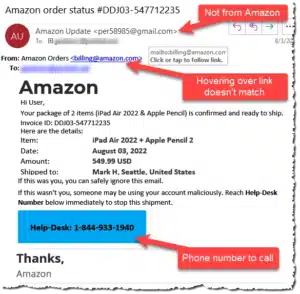
Ever received a suspicious order confirmation or shipping verification? What if I told you that innocent click could cost you more than you bargained for?

https://youtu.be/WPJX4726Htc “Over 97% of American businesses in 2023, operating in a digitally-driven landscape, heavily rely on the Internet for essential functions such as productivity, performance

Is Managed IT Services a Good Fit for my businesses? Facebook Twitter LinkedIn Email In today’s digital age, professional services organizations, including law firms, accountants,

The Hidden Cybersecurity Risks of Remote WorkRemote Employees Are the #1 Threat to Business Security—Here’s What You Need to Know As more professionals work

In the headlines news week on Sept 11, 2023, the giant MGM Grand Hotel & Resorts experienced in Las Vegas had a cyberattack that disrupted many
eSudo Technology Solutions, Inc. Offers Expert Strategies for Mitigating Cybersecurity Threats Reference: eSudo Technology Solutions, Inc. Offers Expert Strategies for IT Service Providers on Mitigating Cybersecurity

Citrix ShareFile is a very known software used by financial professionals, accountants, and law firms to store, transfer or share files with customers. In recent

Ransomware is a type of malicious software that encrypts the victim’s files and demands a ransom for their decryption. LockBit is one of the most